Table of Contents:
Last updated on: June 8, 2022
This article takes a look at the definitions for different intellectual property infringements that brands may be suffering from, and explains them in a way every brand can understand.
Brand abuse is one of those brand protection industry terms that gets used widely – often with some confusion and inconsistency. It’s an umbrella term, generally referring to an attempt to exploit the reputation of a third-party brand for profit, personal benefit or with any malicious intent. This can come in the form of a scam, or fraud, through the unlawful use of one or more elements of a brand’s intellectual property (IP) assets, such as trademarks, copyrighted works, patents, and others.
The brand abuse we’ll look at today includes:
A counterfeit is a product created to look identical to an existing product made by a third party’s brand, and depicts that brand’s trademarked names, logos, symbols and other forms of intellectual property without authorization, with the intention of deceiving customers into thinking the counterfeit is an official item from the genuine brand.
As with a counterfeit, a replica is intended to be an identical copy of an authentic product made by a third party, which infringes on trademark and design IP. The words “replica” and “counterfeit” are often used interchangeably.
Below is a counterfeit Supreme jumper. It copies both the design of an original Supreme product, as well as using the trademarked logo of the authentic brand – the white “Supreme” in a red box.

A look-alike product copies the look and feel of the design of an existing product, such as elements of its trade dress or product branding – similar to counterfeits. The difference between look-alikes and counterfeits is that with look-alikes, there is often no direct infringing on a third party’s trademark.
A look-alike item may be produced independent of the original, with no knowledge of the existing product. However, many other copycats steal other brands’ designs intentionally. The intentionality is discretional and is usually determined through litigation.
In some cases, look-alikes take trademarks from other brands and alter them slightly. They do this to confuse customers, and to take advantage of other, more well-respected brands. For example, a copycat sports brand may call their product Fuma, change KitKat to KatKot, or add a fourth stripe to the Adidas logo. This type of copycat product is commonly produced in areas of weak IP rights laws.
Below is a wide range of Dr. Pepper copycat products, with varying levels of similarity to the original product. These look-alikeh use elements of the authentic Dr. Pepper product packaging design, as well as variations on the famous name.

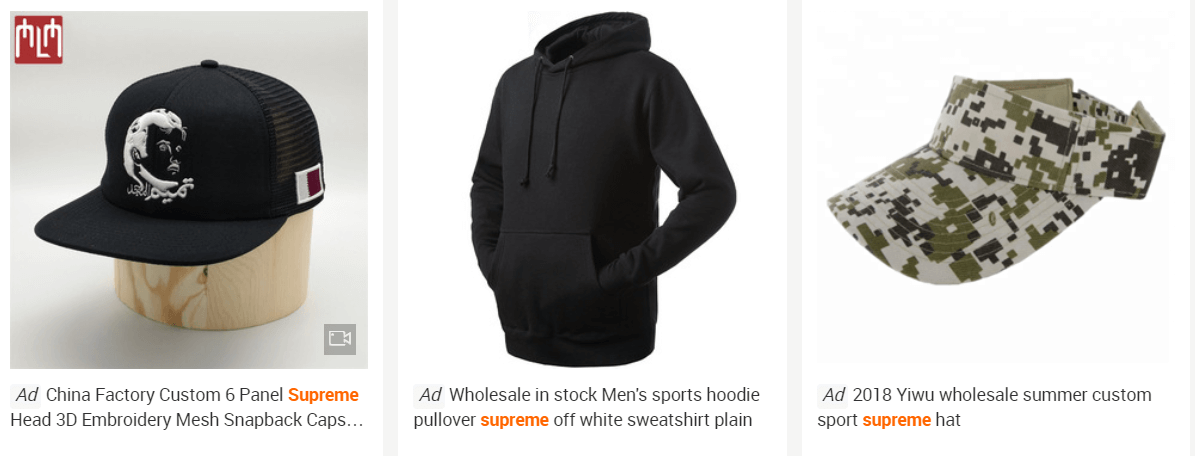
On ecommerce platforms, trademark-infringing listings are those that depict the trademarks of other brands without authorization in the title, images or description of the listing. However, the goods offered in the listing are copies of genuine products, or to products of other brands, meaning the product sold is not counterfeit. Specifically, these listings can be also referred to as “brand name misuse”, or “logo misuse”.
Trademark-infringing listings are used with the intention to pull visitors to their listing, which offers a similar product, rather than to pass the listing as a product provided by a genuine brand. The practise is still considered an infringement on IP, as they use a brand name without authorization.
Here are three trademark-infringing listings found on an online marketplace. Each example uses Supreme’s trademarked names in the title of their listings, but the actual products for sale are look-alikes at worst, or entirely different products.
Design-infringing products are generally created to look like the products of another brand, by copying the distinctive elements of brands. This is done while avoiding the use of any protected trademarks which would establish the product as counterfeit. These products are usually illegal if the copied brand’s products are protected designs. They are created with a similar look and feel to an existing product. As with look-alikes, the intent of infringement is determined through litigation.
Below is just one of many examples of a product copying the famous design of Converse’s Chuck Taylor All-Stars design of shoe. The shoe is unbranded, so there is no trademark, but the similarities between this product and those produced by Converse are clear.

Piracy is the unauthorized reproduction, copying and spreading of copyrighted materials, most often software, ebooks, songs or movies. The Pirate Bay, pictured below, has been a favorite site for copyright pirates in recent years, providing torrent links to films, albums, video games and more.

Copyright-infringing listings on ecommerce tends to refer to sellers using copyrighted photos, text, or other media from an authentic brand to sell a counterfeit product. This is similar to a trademar-infringing listing, as explained above, but instead of using a trademark-protected brand name, the infringer uses images and other text from the authentic brand.
Some products, like those produced by Kiini or David Trubridge, may use copyright protection on their products if they are particularly artful products or don’t currently have trademark or patent protection. There is often significant overlapping with design protections on similar products, as explained in the previous section. While misuse of this IP wouldn’t be considered piracy, nor counterfeit, it is still a copyright infringement.
Trademark squatting is an act of registering or using other people’s brand name and assets in other countries, where the original brand does not yet have a registered mark. They operate in bad faith, in order to gain benefits from original brands or real trademark owners.
Usually, trademark squatters can try to benefit by:
Brand impersonation refers to when a third party claims to be, represent, or be affiliated with an authentic brand without authorisation. It consists of a type of infringement on a brand’s trademark, copyright , or other form of IP that are used to identify the brand as authentic. Brand impersonation is especially common on social media, on fake apps or by using imitation rogue websites.
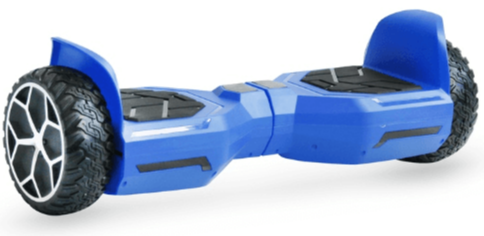
These are products which exactly copy the functionality and mechanism of products protected by utility patents. This form of intellectual property is typically registered to protect inventions, and last for 20 years, in order to promote innovation in technology.
Below is an image of a hoverboard, one of many products that copied the patent-protected design originally created by Shane Chen’s Hovertrax.
Rogue websites infringe on a brand’s IP to turn a profit, and come in a number of forms, which we’ll outline here. A more detailed explanation of this issue, and for protection strategies, take a look at our rogue websites blog post.
You can see below a fake website, accessed when the user types “faecbook.com”, a clear mistyping of Facebook, making this site a clear example of typosquatting. Movielab.com is a different, unaffiliated website, and the website in the image is purely run for bad-faith purposes.
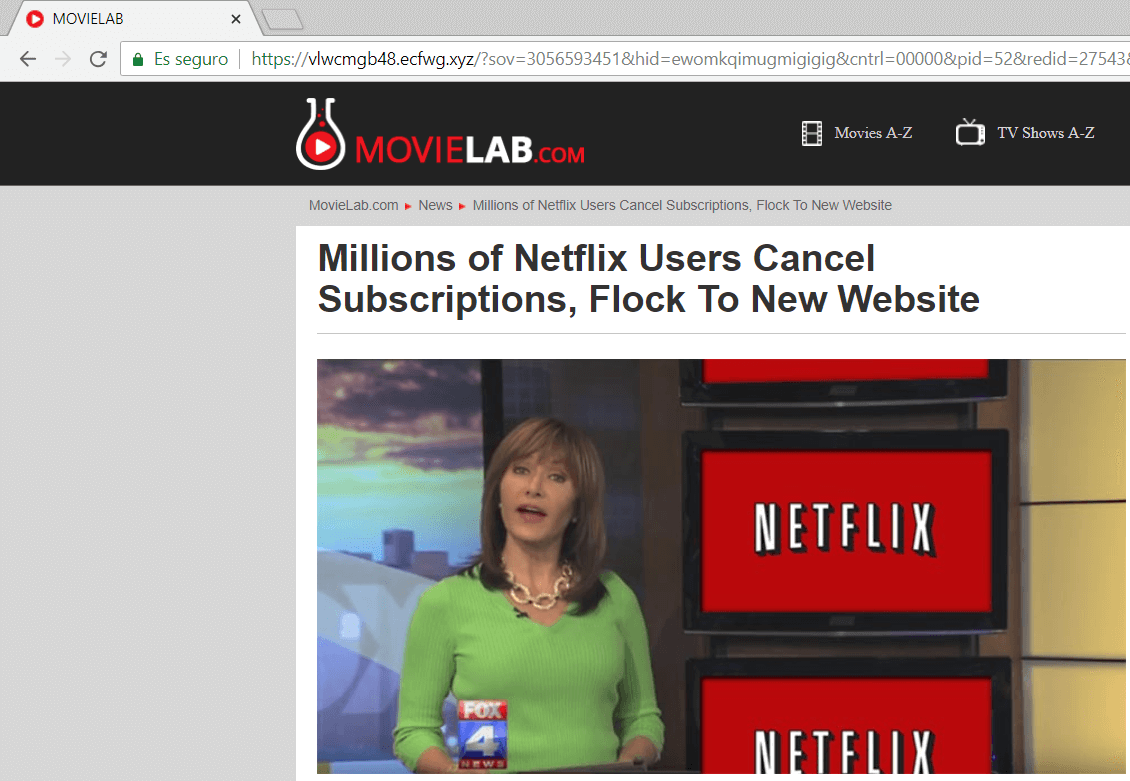
Typosquatting refers to registering slight variations of domain names for popular online websites, with the hope of gaining traffic through mistyping or misspelling errors committed by internet users. Once visitors arrive at the typosquatting website, they are presented with counterfeit products, competing products, or even viruses or scams.
Cybersquatting, commonly referred to as domain squatting, refers to the practise of claiming domain names in order to take advantage of trademarks belonging to someone else, and typically to use those domains in bad-faith intent.
The strategy of profiting from cybersquatting is the same as with trademark squatting. The domain is sold to the trademark owner, or products are counterfeited and sold under the infringing domain, and so on.
Considering how cheap it is to purchase and maintain a domain in today’s world, and how important branding is to many companies, there is a lot of profit to be made from domain resale.